
Risk Assessment in the Supply Chain: Why It Matters, Part 1
It may come across as a bit of a joke to see that a Dutch supermarket recently ran out of cheese as a result of a ransomware attack, but it’s no laughing matter that a single attack could potentially have such a devastating effect on the supply chain. In this instance, the logistics services company “suffered a ransomware attack that encrypted devices on their network.” The result? A disruption in the company’s food transportation and fulfillment operations.
This isn’t uncommon in the age of cyberattacks and vulnerability exploits. In November, cold storage company Americold was hit with a cyberattack that impacted operations, including its phone systems and email, inventory management system, and order fulfillment software. In a business that is heavily reliant on being able to meet shipping deadlines before product spoils, this can result in a significant loss in revenue.
These two examples are becoming increasingly common as food production and agribusinesses use more technology to streamline operations, increase return-on-investment (ROI), and improve processes. However, it’s not enough to simply add technology without first establishing a technology strategy – especially when each piece of the supply chain is wholly dependent on the other.
What is the supply chain?
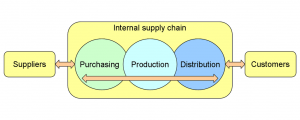
**Wiki Commons Image: ShareAlike 3.0 Unported (CC BY-SA 3.0)
The supply chain consists of the entire process of creating and selling a product. For example, the fresh produce supply chain encompasses the grower, processor, distributor, and retailer (and can go even further into logistics, cooling, packaging procurement, and more). Each and every organization along that chain has a role to play and is an essential piece of the puzzle that starts with a head of lettuce growing in a field to that same head of lettuce being sold in a supermarket.
You can also look at the supply chain in more personal terms. Disruption of it can be felt around the globe. Think about the pandemic and the shutdowns in China that affected the world’s ability to source raw materials and products. If you were building a house, the cost of materials like lumber and steel skyrocketed by as much as 20% to 25% since the start of the pandemic, resulting in significant slowdowns for builders and new construction. And this is just one example of the supply chain at work.
What is risk assessment for the supply chain?
One of the great assumptions of supply chain risk is that it is solely an IT security-related function, but IT needs to be able to coordinate with all departments in a seamless manner. At a minimum, each organization is dependent on the continuity of systems across the supply chain. Purchasing or procurement departments, for example, may have some processes in place for vendor selection criteria to meet related to creditworthiness, qualifications, licensing, and more.
Operationally mature companies may have contracting departments that manage the entire process, but most companies within agribusiness may not understand the level of risk that their supply chain faces without additional resources.
Conducting a supply chain risk assessment within an agriculture-focused company, such as a fresh produce distributor, begins with looking at an organization’s supply chain and mapping it. Where are the dependencies? How do each of our vendors fit into the overall picture? And how do we get from point A to point B? Answering these questions becomes a strong foundation on which to build the next steps in the assessment process.
How can organizations identify vendor risk?
After an organization begins to see its technology strategy as an integral part of the supply chain, it’s time to ask some crucial questions that can help identify potential risk across vendors, such as:
- Who are my vendors? Identify who is involved and at what level.
- Which vendors are critical? If you have a single-source supplier that has a single factory that produces what you need, this can be identified as a potential risk to the organization if that vendor cannot deliver on time.
- How are vendors selected? In some markets, financial validation such as a credit report is required of businesses to be identified as a vendor, but rarely is IT looked at as a critical piece of the decision-making process. As more risk is identified (such as a single-source supplier), this needs to change.
- Which vendors are peripheral? Identify the vendors who might be secondary to the operation and examine the level at which they’re used. Even if there are vendors that you work with only once a quarter or even once a year, their link to your company can make them a risk.
- Do my vendors have a business continuity plan in place? At times, some vendors are in a “just in time” delivery model, which can place significant stress on the supply chain if that source goes down and there is no business continuity plan in place to help get them up and running in a timely manner. This should be a crucial factor in the discussion of vendor risk.
- Do I have alternative vendors in place for critical supplies? We often talk about the idea of “it’s not if, but when” as it relates to a cyberattack. The nature of business and connectivity makes this a real threat, so part of supply chain risk assessment determines how long it will take your company to identify another source for supplies if a supplier goes down.
When working with ZAG, part of determining risk is centered around the adherence to ZAG Standards that are used to measure the client’s security posture. But when you’re working within an industry as dependent on the supply chain as fresh produce, these standards become an integral part of how your vendors should be assessed for potential risk.
Third-party risk assessments, such as those provided by SecurityScorecard, offer continuous cyber risk management for the agribusiness sector that instantly identifies vulnerabilities, active exploits, and advanced cyber threats. But simply identifying vulnerabilities within your supply chain is not enough. Engaging with a trusted partner and IT consultant that can take the results of this assessment and translate the results into actionable insights for your organization can mean all the difference to greater protection across the supply chain.
What comes after the risk assessment?
There’s an adage that is fitting in the realm of supply chain risk: You’re only as strong as your weakest link.
Assessing an organization’s supply chain risk is the first step toward ensuring risk mitigation and business continuity. Once an assessment is conducted, additional considerations must be made alongside other departments to ensure the best possible outcome for the business, such as working with procurement to introduce vendor qualifications. All of this is part of the next phase in the process: supply chain risk management.
We discuss the next steps in the second part of this series, “Risk Management for the Supply Chain: Putting a Plan in Place,” or you can click here to contact us to talk about your supply chain risk.