
Case Study: Markon Cooperative
Markon Cooperative puts the security of its IT systems first with support and guidance from ZAG Technical Services. …

Fraud Awareness: Protecting Executive Leadership
During National Fraud Awareness Week, it’s time to look at protecting executives to protect business …

How to Avoid Charity Scams during Disasters
Criminals and scammers exploit disasters for their own profit. How to avoid being …

Jan. 27 Event: “Reviewing Your IT Security: Have You Done Enough?”
Learn how to identify tech deficiencies, the steps you can take to address vulnerabilities, and the tools to …

Log4j + ZAG: What We’re Doing
ZAG is actively working on identifying and patching integrated vendor systems and applications that leverage the Apache …

Patching Your Systems: The Gift that Keeps on Giving
Patching your systems is a critical piece of the maintenance puzzle, but users must follow best practices to make sure …
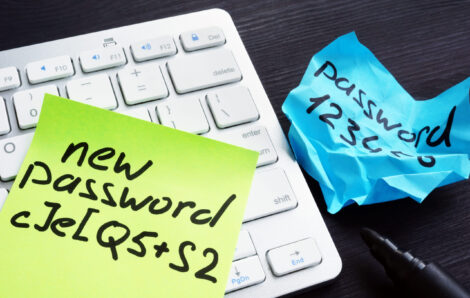
Strong Security Starts with Strong Passwords
It’s all too easy to think passwords are a nuisance—when really they’re essential to keeping your data and your …

PII: Why Your Organization Should Care
Personally identifiable information, or PII, should be protected. But what should organizations do to ensure that it …

ZAG Launches Supply Chain Risk Program to Address Vendor Cyber Vulnerabilities
ZAG launches a new supply chain risk assessment and management program aimed at providing agribusinesses with …

How to Create a Firewall: Best Practices for Protecting Internal Networks
Creating a firewall can help protect your network from unauthorized access. ZAG provides best practices for …

Surveillance Camera Breach Opens Up Discussions Around Third-party IoT Devices
Networked devices can be vectors for cybersecurity threats, making IoT security and vendor selection a priority. …

Password Managers: Protecting Your Personal Logins
Implementing additional password security with password management software can help your business protect its …

Cloud Identity and Access Management, Reducing Security Risk
Learn the benefits of centralized identity and security using IAM solutions. …

Email Security Training, Your First Line of Defense Against Phishing
It's time to implement training for all of your employees to protect your …

IT Security Case Study: One Company, Two Ransomware Attacks
One Company, Two Ransomware Attacks. This company was long overdue for a comprehensive Security Assessment. ZAG was …